The search for business dexterity to effectively change business requires IT to be accepted as the core strength. It is important to have the updated IT infrastructure to support a changing application’s level and complexity. Organizations must embrace this mandatory move by renewing server infrastructure, taking possession of software-defined data center (SDDC) and modernizing their system for IT infrastructure management. Those who do it will inspire business modernity and provide better customer experience with quick, safe, reliable business technology.
For companies competing in today’s digital economy, there is a premium to offer optimized user experiences – all the time and every time – thus extracting the infrastructure’s ultimate flexibility, efficiency, and quality. The digital infrastructure that businesses rely on continues to grow increasingly dynamic and elastic, diverse and dispersed in order to meet these demands. There is a premium for businesses operating in today’s digital environment to offer personalized user experiences – all the time and every moment – while extracting full flexibility, efficiency, and quality from the infrastructure. The visual infrastructures that businesses rely on to maintain must grow increasingly flexible and decentralized, diversified and elastic in order to meet this requirement. Companies usually rely on multiple public clouds, selecting the right services best aligned with each specific case and objective of use. In the situation, containerized, workloads in the position of virtualized workloads are opening up to leverage. IT departments are increasingly adopting approaches to serverless computing. The use of hyper-converged infrastructure continues to grow for companies operating their internal private clouds and on-site business services. With all these different trends emerging, change continues to grow faster, making it difficult to forecast the future. The only thing that seems few is that the atmosphere in nature will only move forward with more hybrids.
Related Post: What is Business Process Management?
The challenge: Lacking hybrid environment visibility
IT departments in control of the quality of the user experience are currently creating new challenges in hybrid environments. The performance and integration of a wide range of infrastructures, including cloud and on-site, traditional and dynamic, can now be uncertain when a customer interacts with the android or the other application such as that. When problems arise, it becomes more arduous to determine what the reason is, where it is and how to put it. Furthermore, this lack of visibility means that IT teams can react to an object only after the experience of customers is inadequate. Businesses made to be able to easily track performance in the digital economy and achieve the insights needed to spot trends in issues and address issues before the customer ever considers a problem. IT departments are forced to run numerous monitoring tools as there is no deployed platform capable of providing full-environment coverage. Since organizations are using various monitoring software, the IT department should devote a large amount of time to the installation and management of devices and overall information from across systems to produce reports. Investments in excess technology and cloud services are wasted when necessary or cash. These disjointed toolsets impede flexibility substantially in the end. Due to the time takes to carry out the necessary monitoring capabilities, software rollouts are delayed. Likewise, it takes to much time to adopt new technology as a modern testing system has to be procured, designed and deployed.

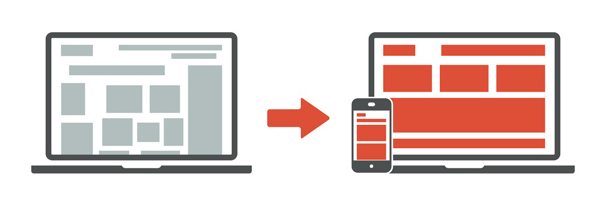
Recent Infrastructure Important Mandatory
Configuration based on complex policies: an integrated default framework for controlling deployments. Unified monitoring and analytics: a unified out of the box solution that includes the entire IT infrastructure; on-site infrastructure, cloud services, or both hybrid.
Extensibility: a simplified perspective for new technology integration and support.
Contextual Intelligence: improved tools for tracking networks with potential for artificial intellect-driven analysis; AIOps
Automation: Automated technologies for exploration and implementation that adapt to changing environments.
Related Post: Why Businesses Must Integrate Artificial Intelligence [AI]?
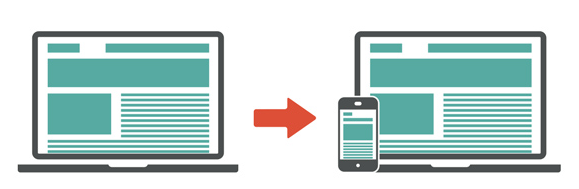
Ouriken’s Infrastructure Management services include monitoring and tracking tools to effectively manage business-critical applications. We are a standalone web design and digital agency. We design and implements powerful solutions for small and medium businesses in technology, business, and operations.
[contact-form][contact-field label=”Name” type=”name” required=”true” /][contact-field label=”Email” type=”email” required=”true” /][contact-field label=”Website” type=”url” /][contact-field label=”Message” type=”textarea” /][/contact-form]